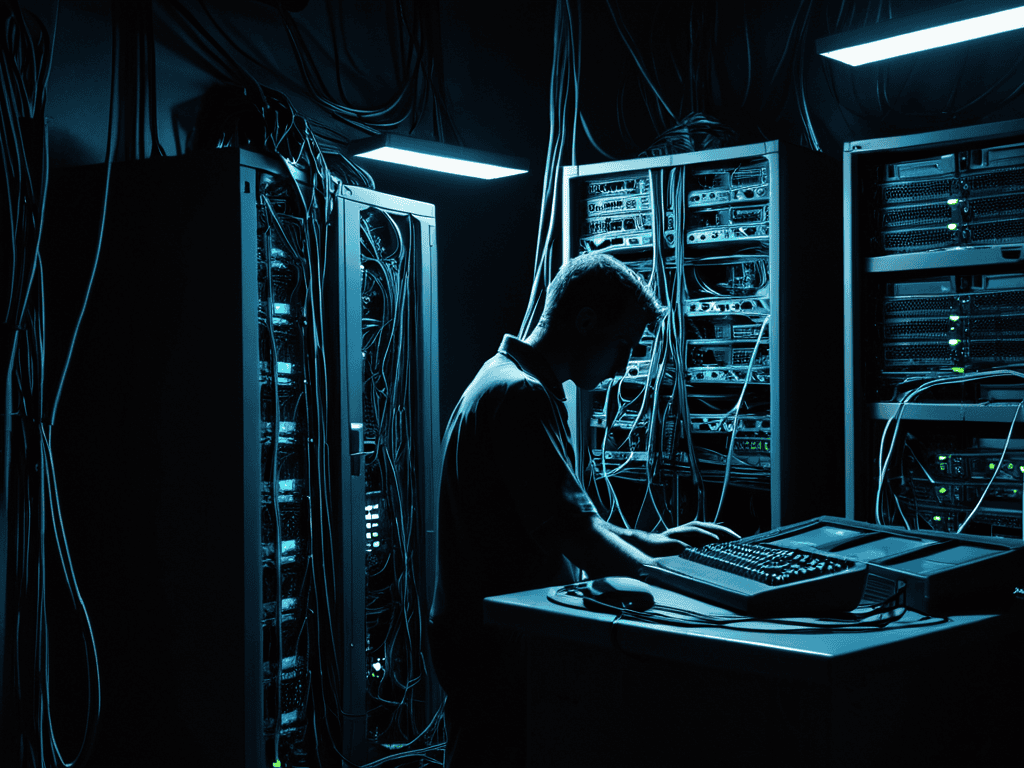
I still remember the day our company’s entire system crashed due to a Shadow IT Risks debacle. It was like a ticking time bomb had finally gone off, and we were left to pick up the pieces. The so-called “experts” told us that we needed to invest in even more complicated and expensive solutions to mitigate these risks. But I knew that was just a bunch of hype. We didn’t need more bells and whistles; we needed a straightforward, no-nonsense approach to dealing with the Shadow IT Risks that were lurking in the shadows.
In this article, I’ll cut through the clutter and give you the lowdown on how to really tackle Shadow IT Risks. I’ll share my personal experience and the lessons I’ve learned from being in the trenches. You won’t find any fluff or jargon here, just honest, experience-based advice on how to identify and mitigate these risks. My goal is to empower you with the knowledge and tools you need to take control of your organization’s IT security, without breaking the bank or getting bogged down in unnecessary complexity. So, let’s get started and shine a light on the Shadow IT Risks that have been hiding in plain sight.
Table of Contents
Shadow It Risks Lurk

As you navigate the complex landscape of shadow IT risks, it’s essential to stay informed about the latest threats and mitigation strategies. One often overlooked aspect of this is the human factor, where employees may unintentionally compromise security by using unauthorized cloud services or devices. To better understand these risks and how to address them, I recommend checking out the resources available at siesuchtsex, which offer a wealth of information on cloud security best practices and how to implement them effectively within your organization. By taking a proactive approach to educating yourself and your team, you can significantly reduce the likelihood of a shadow IT-related breach and create a more secure, compliant work environment.
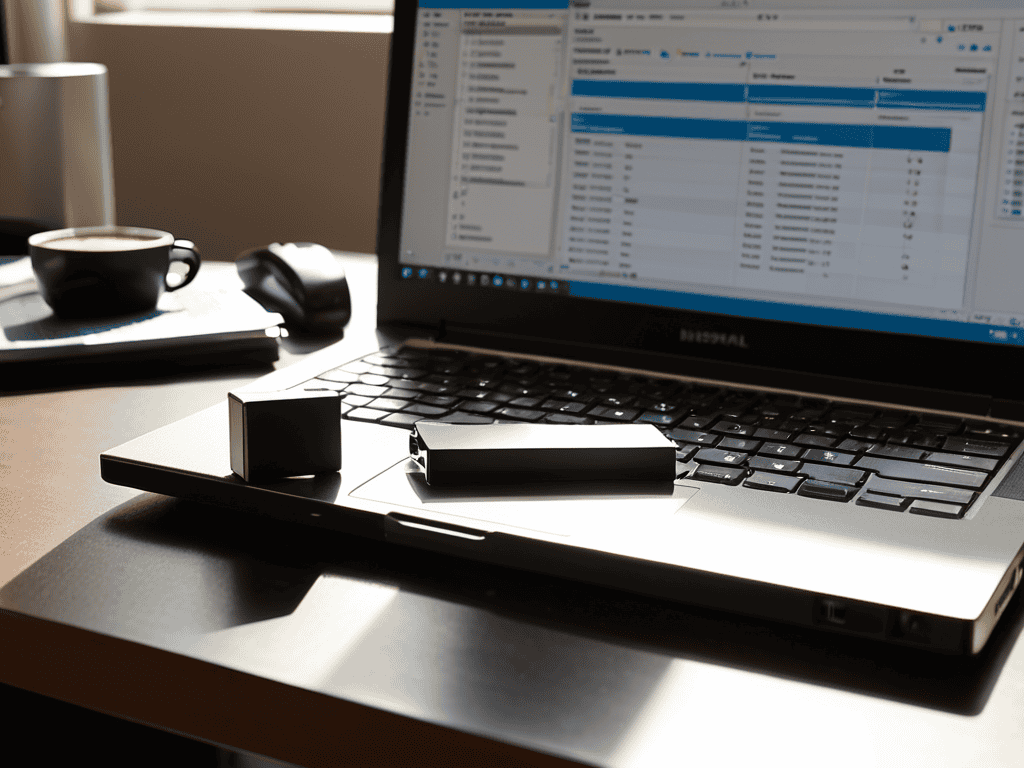
The presence of unauthorized devices and applications within an organization’s network can lead to significant sensitive data exposure. This is because these devices and applications may not adhere to the company’s cloud security threats protocols, making it easier for hackers to gain access to sensitive information. As a result, it is crucial for organizations to implement effective unapproved device management strategies to mitigate these risks.
Effective insider threat detection is also vital in identifying and preventing potential security breaches. This can be achieved through regular compliance and risk assessment audits, which help to identify vulnerabilities and weaknesses in the organization’s security framework. By addressing these vulnerabilities, organizations can reduce the risk of security breaches and protect their sensitive data.
The use of shadow IT discovery tools can also help organizations to identify and manage unauthorized devices and applications within their network. These tools provide a comprehensive overview of the organization’s IT infrastructure, allowing administrators to detect and respond to potential security threats in a timely and effective manner. By leveraging these tools, organizations can strengthen their security posture and reduce the risk of cloud security threats.
Cloud Security Threats Uncovered
As we delve into the world of shadow IT risks, it’s essential to consider the cloud security threats that are often overlooked. These threats can manifest in various ways, from data breaches to unauthorized access, and can have devastating consequences for an organization.
The use of unauthorized cloud services can create vulnerabilities that can be exploited by malicious actors, leading to a loss of sensitive data and intellectual property.
Sensitive Data Exposure Dangers
When sensitive data falls into the wrong hands, it can lead to catastrophic consequences. This is especially true in the context of shadow IT, where unauthorized cloud services and apps can create vulnerabilities that are often overlooked.
The use of unsecured networks can exacerbate these risks, making it easier for hackers to intercept and exploit sensitive information.
Mitigating Shadow It Risks

To effectively mitigate the risks, organizations must first acknowledge the existence of unapproved devices and software within their network. This is where cloud security threats come into play, as employees may be using personal cloud storage or unauthorized applications to perform their tasks. By implementing a robust compliance and risk assessment framework, companies can identify and address these vulnerabilities before they escalate into full-blown crises.
Another crucial aspect of mitigating these risks is insider threat detection. This involves monitoring employee behavior and identifying potential security breaches before they occur. By leveraging shadow IT discovery tools, organizations can gain visibility into unauthorized devices and applications, and take swift action to prevent sensitive data exposure. This proactive approach can help prevent data breaches and protect sensitive information from falling into the wrong hands.
By taking a proactive stance on unapproved device management, organizations can significantly reduce the risk of security breaches. This involves implementing strict policies and procedures for device usage, as well as providing employees with secure and authorized alternatives to personal devices. By doing so, companies can minimize the risk of cloud security threats and ensure a safer, more secure working environment for all employees.
Compliance Assessment With Discovery Tools
To effectively assess compliance, organizations can leverage discovery tools to identify and categorize unauthorized IT systems and services. This proactive approach enables companies to pinpoint potential vulnerabilities and take corrective action before they become major issues. By using these tools, businesses can ensure they are meeting regulatory requirements and reducing the risk of non-compliance.
Regular compliance assessments using discovery tools can help organizations stay ahead of potential problems, allowing them to address shadow IT risks before they escalate into full-blown crises.
Insider Threat Detection Strategies
To effectively detect insider threats, organizations must implement a combination of proactive monitoring and user education. This approach helps to identify potential security risks before they escalate into full-blown incidents. By keeping a close eye on user activity and providing regular training, companies can reduce the likelihood of insider threats.
A key component of insider threat detection is establishing a culture of transparency and trust within the organization. This encourages employees to report suspicious activity without fear of reprisal, allowing for swift action to be taken when necessary.
Taming the Shadow: 5 Essential Tips to Minimize IT Risks
- Implement a Zero-Trust Model to Limit Unapproved App Access
- Conduct Regular Cloud Security Audits to Uncover Hidden Threats
- Develop a Culture of Transparency to Encourage Employees to Report Unauthorized IT Use
- Utilize Automated Discovery Tools to Identify and Mitigate Sensitive Data Exposure
- Establish Clear Policies and Procedures for Sanctioned IT Solutions to Reduce Insider Threats
Key Takeaways to Tackle Shadow IT
Tackling shadow IT requires a proactive approach, including regular audits and employee education to prevent unauthorized software and services from compromising your organization’s security
Effective mitigation strategies involve a combination of insider threat detection, compliance assessments, and the implementation of discovery tools to uncover and manage cloud security threats
By understanding the dangers of shadow IT, such as sensitive data exposure, and taking concrete steps to address these risks, organizations can significantly reduce the likelihood of security breaches and protect their valuable assets
The Shadow IT Reality Check
Shadow IT is like a silent predator, lurking in the darkest corners of your organization, waiting to pounce and unleash a world of chaos – and the most terrifying part is, you might not even know it’s there until it’s too late.
A Concerned IT Specialist
Conclusion
In conclusion, shadow IT risks are a pressing concern that organizations can no longer afford to ignore. We’ve explored how these risks lurk in the shadows, threatening the very foundation of our digital infrastructure. From cloud security threats to sensitive data exposure dangers, the potential consequences of unchecked shadow IT are dire. By implementing effective mitigation strategies, such as insider threat detection and compliance assessment, organizations can reduce their exposure to these risks and protect their assets.
As we move forward in this digital landscape, it’s essential to remain vigilant and proactive in addressing emerging threats. By acknowledging the dangers of shadow IT and taking bold steps to mitigate them, we can create a safer, more secure environment for our organizations to thrive. Let’s take the first step towards a more resilient future, one where technology serves us, not the other way around. The time to act is now, and the reward will be a safer digital tomorrow.
Frequently Asked Questions
What are the most common types of shadow IT risks that organizations should be aware of?
The most common types of shadow IT risks include unauthorized cloud services, unapproved mobile apps, and rogue networks, which can lead to data breaches, malware infections, and compliance issues, ultimately compromising an organization’s security and integrity.
How can employees be educated to avoid using unauthorized cloud services and putting company data at risk?
Educate employees by explaining the risks of unauthorized cloud services in simple terms, and provide clear guidelines on approved tools and platforms. Regular training sessions and awareness campaigns can also help, as well as leading by example from top management to foster a culture of security.
What are the consequences of not mitigating shadow IT risks and how can they impact an organization’s reputation and bottom line?
Failing to mitigate shadow IT risks can lead to devastating consequences, including data breaches, financial losses, and reputational damage. If sensitive information falls into the wrong hands, it can tarnish your organization’s reputation and impact the bottom line, ultimately affecting customer trust and loyalty.











+ There are no comments
Add yours