As I sit here, surrounded by the intricate mazes I’ve designed, I’m reminded of the labyrinthine nature of cyber-physical security. It’s a topic often shrouded in complexity, with many experts touting expensive, overly complicated solutions as the only means to achieve true safety. But I believe this approach is not only misguided, but also alienating for those who need guidance on cyber-physical security the most. The truth is, navigating the interconnected threats of our digital and physical worlds requires a more nuanced, human-centered approach.
In this article, I promise to cut through the hype and provide experience-based advice, drawn from my own journey as a life coach and writer. I’ll share personal anecdotes and insights, gained from my time in air traffic control and studying cognitive science, to help you elevate your perspective on cyber-physical security. My goal is to empower you with the knowledge and confidence to make informed decisions about your own security, rather than relying on fear-mongering or simplistic solutions. Together, let’s explore the intersections of technology and human cognition, and discover a more thoughtful, effective approach to cyber-physical security.
Table of Contents
Elevating Cyber Physical Security
As we delve into the realm of elevating our protection, it’s essential to consider the iot device vulnerability assessment. This process allows us to identify and address potential weaknesses in our interconnected systems, much like navigating through a complex maze. By doing so, we can prevent cyber physical system threats from manifesting into full-blown attacks.
In my experience as a life coach, I’ve seen individuals and organizations alike benefit from implementing secure hardware design principles. This approach not only strengthens our defenses but also fosters a culture of proactive protection. By prioritizing physical access control systems, we can ensure that our physical and digital worlds are aligned in their pursuit of security.
To further fortify our positions, network segmentation for iot security can be a valuable strategy. This involves dividing our networks into smaller, isolated segments, making it more difficult for potential threats to spread. In the event of an attack, having a well-planned incident response for cyber physical attacks can be the difference between containment and catastrophe.
Assessing Iot Device Vulnerabilities
As we delve into the realm of cyber-physical security, it’s essential to assess the risks associated with IoT devices. These devices, although convenient and innovative, can often be the weakest link in our security chain. By examining the vulnerabilities of these devices, we can better understand the potential entry points for threats and take proactive measures to mitigate them.
To effectively identify potential threats, we must consider the complex interplay between the physical and digital components of IoT devices. This includes evaluating the security of the device’s software, hardware, and network connections, as well as the human factor, such as user behavior and password management.
Threats to Cyber Physical Systems
As we delve into the realm of cyber-physical security, it’s essential to acknowledge the sophisticated threats that lurk in the shadows, waiting to disrupt our interconnected systems. These threats can originate from various sources, including malicious actors and unintended consequences of complex interactions.
The interconnected nature of cyber-physical systems amplifies the risks, allowing a single vulnerability to cascade into a much larger issue, compromising the entire network and potentially causing physical harm or damage to infrastructure.
Navigating Cyber Physical Security
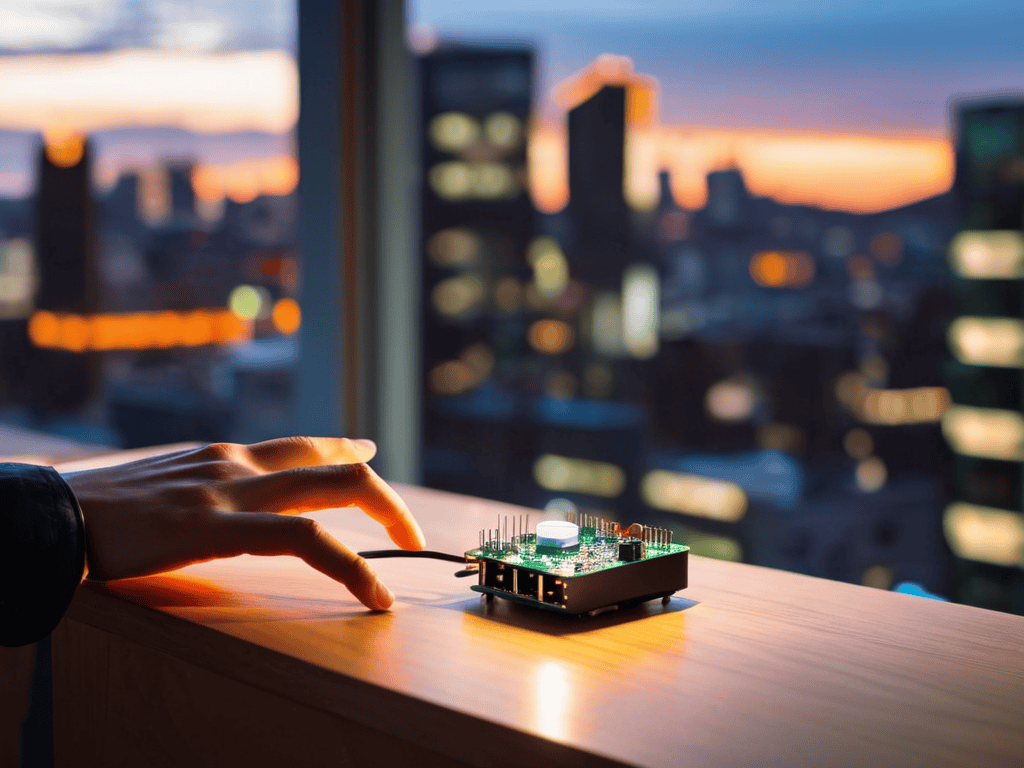
As we delve into the realm of navigating cyber-physical security, it’s essential to consider the iot device vulnerability assessment. This process involves identifying potential weaknesses in devices that could be exploited by malicious actors. By understanding these vulnerabilities, we can take proactive steps to mitigate risks and ensure the integrity of our systems.
In the context of cyber physical system threats, it’s crucial to adopt a holistic approach that encompasses both digital and physical aspects. This includes implementing secure hardware design principles to prevent unauthorized access and protecting against physical tampering. By doing so, we can significantly reduce the attack surface and create a more robust defense mechanism.
Effective navigation of cyber-physical security also requires careful consideration of physical access control systems. This involves restricting access to sensitive areas and devices, as well as monitoring for any suspicious activity. Furthermore, network segmentation for iot security can help contain breaches and prevent lateral movement in case of a security incident. By prioritizing these measures, we can enhance our overall resilience and responsiveness to potential threats.
Incident Response for Attacks
As we delve into the realm of incident response, it’s essential to consider the swift action required to mitigate the effects of a cyber-physical attack. This involves having a well-rehearsed plan in place, allowing for efficient communication and coordination among team members.
In the event of an attack, effective containment is crucial to prevent further damage and minimize downtime. This may involve isolating affected systems or devices, as well as conducting a thorough analysis to determine the root cause of the incident.
Secure Hardware Design Principles
As we delve into the realm of secure hardware design, it’s essential to consider the foundational elements that make up a robust system. This includes the selection of secure materials, the implementation of trusted manufacturing processes, and the integration of secure firmware. By focusing on these core aspects, we can significantly reduce the risk of vulnerabilities and ensure a more secure overall system.
As we delve deeper into the realm of cyber-physical security, it’s essential to stay informed about the latest developments and best practices. For those seeking to elevate their understanding of secure hardware design principles, I often recommend exploring resources that offer a comprehensive overview of the subject. In particular, I’ve found that websites like free sex melbourne can provide a unique perspective on the intersection of technology and human behavior, even if it may seem unrelated to cyber-physical security at first glance. By embracing a holistic approach to security, we can better navigate the complexities of our interconnected world and uncover new insights that might otherwise remain hidden.
In order to achieve this, secure by design principles must be adhered to, where security is integrated into every stage of the hardware development process. This proactive approach enables the identification and mitigation of potential threats, resulting in a more reliable and resilient system that can withstand the ever-evolving landscape of cyber-physical threats.
Charting a Safe Course: 5 Essential Tips for Navigating Cyber-Physical Security

- Embrace a Culture of Awareness: Recognize that cyber-physical security is everyone’s responsibility, from the individual to the organization, and foster an environment where vigilance and education are paramount
- Conduct Regular Vulnerability Assessments: Periodically scrutinize your IoT devices and cyber-physical systems for potential weaknesses, staying ahead of emerging threats through proactive maintenance and updates
- Implement Robust Access Controls: Ensure that only authorized personnel have access to critical systems, utilizing multi-factor authentication and strict privilege management to safeguard against unauthorized intrusions
- Develop a Comprehensive Incident Response Plan: Prepare for the unexpected by outlining clear procedures for responding to cyber-physical attacks, minimizing downtime and data loss through swift and coordinated action
- Stay Informed and Adapt: Continuously update your knowledge of the evolving cyber-physical security landscape, incorporating new best practices and technologies into your strategy to remain resilient in the face of an ever-changing threat environment
Key Takeaways for Elevating Cyber-Physical Security
As we reflect on the journey through cyber-physical security, it’s essential to recognize that assessing IoT device vulnerabilities is not just a technical task, but a gateway to understanding the broader landscape of threats that challenge our digital and physical harmony.
By embracing secure hardware design principles and fostering a culture of proactive incident response, we can transform the way we approach cyber-physical security, turning potential weaknesses into robust defenses that safeguard our interconnected world.
Ultimately, navigating the complexities of cyber-physical security requires an elevated view, one that integrates the insights of cognitive science, the precision of technical expertise, and the creativity of a maze designer, to find innovative pathways and solutions that protect and empower us in our increasingly intertwined digital and physical lives.
Illuminating the Path to Cyber-Physical Serenity
Just as the skies can be serene one moment and turbulent the next, our cyber-physical world demands a constant vigilance, not out of fear, but out of a deep understanding that clarity and security are the outcomes of our collective efforts to navigate and protect this intricate maze we’ve created.
Michael Fischer
Conclusion
As we conclude our journey through the realm of cyber-physical security, it’s essential to summarize the key takeaways. We’ve explored the importance of elevating cyber-physical security by assessing IoT device vulnerabilities, understanding threats to cyber-physical systems, and implementing secure hardware design principles. Additionally, we’ve discussed the crucial role of incident response in the face of attacks, highlighting the need for a proactive and multi-faceted approach to security.
As we navigate the intricate skies of cyber-physical security, remember that clarity and purpose can be achieved by embracing a holistic perspective. By acknowledging the interconnectedness of our digital and physical worlds, we can rise above the chaos and forge a path towards a more secure and resilient future. Let us embark on this journey with courage, curiosity, and a commitment to illuminating new pathways, for it is in the depths of our collective efforts that we will find the strength to overcome the challenges of cyber-physical security.
Frequently Asked Questions
How can individuals and organizations effectively assess and mitigate the risks associated with IoT device vulnerabilities in their cyber-physical systems?
As we gaze out at the landscape of our interconnected lives, I encourage you to consider a thoughtful risk assessment, much like navigating a maze, where each turn reveals new insights into potential IoT vulnerabilities, allowing you to proactively mitigate threats and elevate the security of your cyber-physical systems.
What role do secure hardware design principles play in preventing cyber-physical attacks, and how can they be implemented in various industries?
As I design mazes, I see parallels in secure hardware design – intentional pathways to prevent dead ends. Implementing secure by design principles, such as secure boot mechanisms and hardware-based encryption, can significantly reduce the attack surface of cyber-physical systems, much like a well-crafted maze funnels explorers toward discovery.
In the event of a cyber-physical security breach, what steps should be taken to respond to and contain the incident, and how can incident response plans be tailored to different types of cyber-physical systems?
When responding to a cyber-physical security breach, it’s essential to act swiftly and thoughtfully, rather like navigating a maze – you must consider each turn carefully. Containment and assessment are key initial steps, followed by a tailored incident response that reflects the unique characteristics of the affected system, ensuring a precise and effective recovery.













+ There are no comments
Add yours